Russia’s recent attacks on Ukraine’s critical infrastructure have severely impacted Ukraine’s populace and businesses. Could a cyber attack cause even more painful disruption to your business? What about a cyber attack on the electric grid?
Your business may or may not be at high risk from bombings, but cyber attacks on critical infrastructure including the electric grid could be devastating, especially if your electric grid has cybersecurity vulnerabilities! Ernie Hayden MIPM CISSP GICSP(Gold) PSP, award-winning author of Critical Infrastructure Risk Management: The Definitive Threat Identification and Threat Reduction Handbook (ASIS International 2021 Book of the Year) warns us of risks to your enterprise from electric grid disruption and discusses electric grid vulnerabilities recently highlighted by the US General Accounting Office (GAO).
Remember the Northeast blackout of 2003? Some businesses were without electricity for up to four days. “The blackout’s proximate cause was a software bug in the alarm system at the control room of FirstEnergy, an Akron, Ohio–based company, which rendered operators unaware of the need to redistribute load after overloaded transmission lines drooped into foliage. What should have been a manageable local blackout cascaded into the collapse of much of the Northeast regional electricity distribution system. [Source: Wikipedia]”
I’m reminded of just a few years ago, when a macroburst storm hit my small town. 10,000+ trees and 1,000+ utility poles went down. Most roads were impassable for several days. Power, internet, and telephone service took almost two weeks to be mostly restored. Residents and businesses suffered severe damage and loss. I was fortunate to have been prepared with a large generator and backup wireless internet, but most of my town fared far worse. Many businesses were devastated, from local merchants to larger operations. While this event was not a cyberattack, I recall thinking at the time about how many ways my family and business could suffer from a longer-term loss of electric power, especially while observing the effect on our friends, neighbors, and local businesses.
- Philip Jan Rothstein, FBCI
=============================================
As this blog is being written, the Russian military is systematically destroying Ukraine’s electricity infrastructure. In a recent Reuters news article about the war in Ukraine, a Ukrainian spokesman observed, “It is important to understand that Russian terrorists will try to use the cold as their weapon,” Prime Minister Denys Shmyhal said recently. “In their sick imagination, Ukrainians sitting for several hours without electricity is a victory. They think that this way they will force us to surrender. This will not happen.” Essentially, the Russians are “weaponizing winter.”
Lessons learned from previous electric grid cyber attacks and cybersecurity vulnerabilities
This isn’t the first time the Russians have attacked Ukraine’s electric grid or have exposed vulnerabilities to their critical infrastructure. Take a look at the history of Ukraine and how Russia has used Ukraine’s electric grid as a test bed. In the first instance, two days before Christmas on December 23, 2015, the Russians hacked and shut down part of the Ukraine power grid. This attack affected ~230,000 consumers for about one to six hours. Again, late in the evening on December 16, 2016, the Russians hacked Ukraine’s electric grid around the capital Kyiv. The hack resulted in a shutdown of the grid for just over an hour and cut one-fifth of the city’s power consumption at that time of night.
Both of these attacks were by a nation-state against a country in the winter, when power is especially important for heating businesses, government offices, and homes. Such attacks were relatively brief; however, they were a demonstration that the electric grid can be shut down by outside cyber-attacks.
Even though these events were in Europe – far from the US – we should pay attention to ways the electric grid can be negatively impacted, i.e., shut down, disabled, or “weaponized.”
Where would all the nation’s infrastructure be if we didn’t have a reliable electric grid? Motors spinning water pumps would not spin. Factories could not manufacture. Refineries could not refine products. Offices and homes would be without heating or cooling.
Protecting your electric grid from cybersecurity vulnerabilities and cyber attacks
During the week of October 10, 2022, the United States Government Accountability Office (GAO) published a short blog highlighting an overview of the nation’s electric grid and a few GAO reports that may be helpful to help guide protection of the grid from attack.
Here is a graphic from the US GAO to help you get a high-level view of the electric grid:
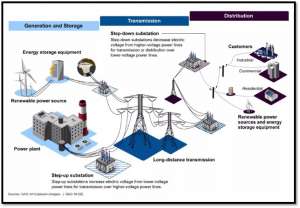
Power is first generated, then sent via high voltage transmission wires over long distances. The voltage is ultimately stepped down/reduced and locally delivered to businesses, schools, and homes via the distribution network.
The transmission system is divided into three distinct interconnected transmission networks covering the contiguous United States plus some parts of Canada and Mexico. The graphic below from the US Department of Energy shows how the transmission grid is divided into the western states, Texas, and eastern states:
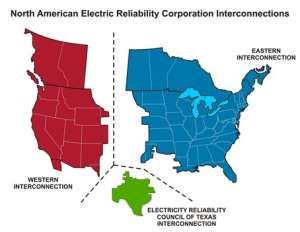
According to the US GAO, there are several points of vulnerability in the U.S. system of electricity grids. For example, electric distribution systems — which carry electricity from transmission systems to consumers — have grown more at risk, in part because their operational technology (think industrial controls running the grid’s circuit breakers and voltage regulators) increasingly allows remote access and connections to business networks by cyber attackers. This could allow threat actors to access those systems and potentially disrupt operations. For instance, nations and criminal groups pose the most significant cyber threats to U.S. critical infrastructure according to the Office of the Director of National Intelligence (ODNI) 2022 Annual Threat Assessment. These threat actors are increasingly capable of attacking and disrupting the grid. The threat actors could be nation-states in a similar vein as Russia attacking Ukraine.
GAO Oversight of Electric Grid Cybersecurity Vulnerabilities
In the past few years, the GAO has been performing reviews and assessments of the nation’s electric grid and the protective actions provided by the transmission and distribution grid operators.
In September 2019 the GAO released a report entitled Critical Infrastructure Protection: Actions Needed to Address Significant Cybersecurity Risks Facing the Electric Grid (GAO 19-332). The GAO observed the following in this report:
“Although the Department of Energy (DOE) has developed plans and an assessment to implement a federal strategy for addressing (transmission) grid cybersecurity risks, these documents do not fully address all of the key characteristics needed for a national strategy. For example, while DOE conducted a risk assessment, that assessment had significant methodological limitations and did not fully analyze grid cybersecurity risks. One such key limitation was that the assessment used a model that covered only a portion of the grid and reflected how that portion existed around 1980. Until DOE has a complete grid cybersecurity plan, the guidance the plan provides decision-makers in allocating resources to address those risks will likely be limited.
Additionally, in March 2021, the GAO released the following report: Electricity Grid Cybersecurity: DOE Needs to Ensure Its Plans Fully Address Risks to Distribution Systems (GAO 21-81). The scope of the GAO report is only focused on the distribution network – i.e., the electric grid that is “closer” to businesses, homes, schools, factories, etc. The GAO observes that the distribution systems are becoming more vulnerable to cyberattacks, again in part because of the introduction and reliance on industrial control systems increasingly allowing remote access and connection to business networks. However, the GAO continues to note, “…the scale of potential impacts from such attacks is not well understood.”
Also, as stated in the GAO report:
The Department of Energy is working on the energy sector portion of the national cybersecurity strategy, but it has focused its efforts more on risks facing the grid’s generation and transmission systems.
This limited review by the DOE is made more complicated because distribution utilities are generally not subject to mandatory federal cybersecurity standards and instead are governed by state public utility commissions or local electric utility boards.
The challenge is not necessarily a technical hurdle but instead is one of responsibility and governance of the respective sections of the electric grid – generation, transmission, or distribution.
Summary of electric grid cybersecurity vulnerabilities and protecting critical infrastructure
The situation in Ukraine could be a wake-up call for the US electric grid operators and regulators. Of note, the Federal Energy Regulatory Commission (FERC) regulates the interstate transmission of electricity. FERC has approved mandatory grid cybersecurity standards; however, the GAO observes FERC has not taken steps to ensure that those standards fully capture federal guidance for critical infrastructure cybersecurity. For example, and similar to the above, the standards do not include a full assessment of cybersecurity risks to the grid. Even the GAO recommendations in 2019 have not been implemented by the federal, state, or local entities and thus the grid remains vulnerable to advanced cyber-attacks.
Finally, in March 2021, the GAO found the federal government does not have a good understanding of the scale of the potential impacts of attacks facing the distribution systems. After identifying this vulnerability in the distribution systems, the GAO recommended the Department of Energy (DOE) and the Department of Homeland Security, state, and industry partners address risks to the distribution systems and not leave the vulnerability remediation to the local level.
Understanding how the nation’s electric grid is built and governed is important knowledge for all federal, state, and local leaders so they can help implement more holistic regulations that address grid vulnerabilities. Also, the lessons learned in the Russian attacks on the Ukraine power grid in 2015 and 2016 – as well as today’s physical attacks on Ukraine’s electric grid during the war – should be used to guide decisions by the federal and state regulators and US electric grid operators on ways to harden their electric control systems both in the cyber sense and physically.
=============================================
Ernie Hayden, MIPM, CISSP, GICSP(Gold), PSP is a highly experienced and seasoned technical consultant, author, speaker, strategist, and thought leader with extensive experience in the power utility industry and critical infrastructure protection and risk assessment. Hayden is a certified physical and cyber security expert with specific expertise in industrial controls security.
Ernie is the author of the new book, Critical Infrastructure Risk Assessment: The Definitive Threat Identification and Threat Reduction Handbook.
VOTED ASIS INTERNATIONAL SECURITY INDUSTRY BOOK OF THE YEAR!
Click HERE to receive a free chapter!
In this free chapter — The Power of the Observation — you will discover:
- An overview of the concept of an “observation.”
- The primary elements included in the observation as well as its format.
- Fundamental considerations when performing and documenting the observation, including the power of one’s influence on the actions being observed, the need for critical thinking, and considerations on how the observation supports the risk assessment.